What if your biggest business decisions were based on a lie? Right now, companies are making nearly $1 trillion in choices based on market research that’s over 40% fake. Bots and fraudulent users are skewing your data, leading you to build products for people who don’t actually exist. You need to know who you’re listening to. Face verification will provide the critical filter that separates real human feedback from automated noise. This ensures the insights you gather are authentic, protecting your strategy and making your next move the right one.
That’s why we signed onto the consumer Data Quality Pledge and why we created Verify, which combines cutting-edge AI technology and lightweight facial verification to fight bots and tackle user fraud dramatically better than CAPTCHA and other solutions.
Verify ensures that collected consumer data remains untainted by many issues, including fake engagement from bots, click farms, and professional respondents masquerading as other personas. This will provide advertisers with an accurate and quality sample every time.
We are constantly exploring expanded use cases for Verify and recently demonstrated some impressive results combining it with Realeyes’ PreView ad testing solution. PreView provides attention & emotional engagement AI-driven insights that guide creative adjustments during the creative production process.
Our hypothesis was that the business decision made based on the results of any market research is wrong if the sample quality is low.
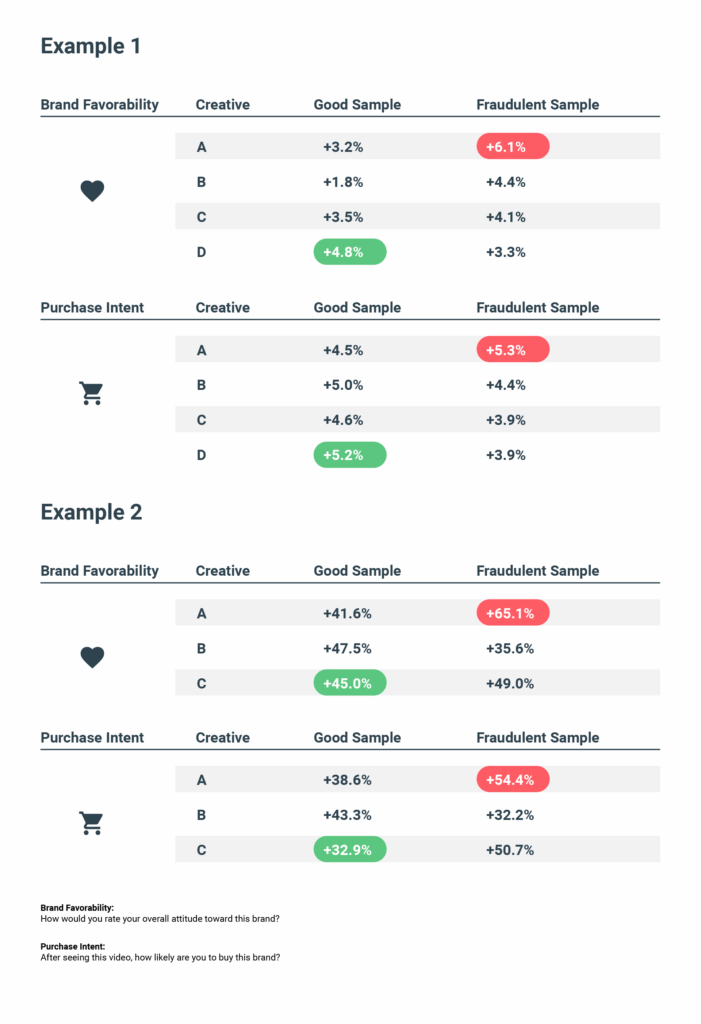
We tested four ads from a home furnishing provider and three from a financial services firm to identify which ads scored highest in brand favorability (how the person would describe their overall attitude toward the following tax preparation software services) and usage intent (how likely the person was to make a purchase).
Before viewing the ads, people had to go through the Verify facial verification to differentiate high quality respondents from fraud, such as either robots or duplicate viewers or misrepresented demographic information.
Verify is designed to proactively filter out fraud in real-time before it reaches the survey environment, but for this test we let it through to see how it would impact the PreView results. We then compared the survey results by comparing the full sample size against those who were verified by Verify to be unique quality users that fit the target demographics.
The results clearly demonstrated that panel quality does affect the insights and outcomes of consumer insights market research — when filtering the data on quality users (filtering out bots, duplicates and demographic fraudsters), the brands would have chosen a different ad to run.
For instance, fraudulent or unacceptable quality users scored an ad with a brand favorability score +6.1% whereas quality users scored that +3.2%, creating an overall score of +4.3%. By including bots and fraudulent users, the company would select this as the top-performing ad. But if you removed those false results, it was actually the third-worst performing ad out of four.
The same ad, when including fraudulent users, scored highest in usage intent, which refers to how likely the recipient is to use the company’s services. It finished last when only scoring acceptable users.
What does that mean? For example, perhaps a company should use the CTA with the female hero and the red car, but flawed data tells them instead to use a male facing a sunset instead.
The results demonstrated just how important Verify is to the ad-testing landscape. Failing to eliminate fraudulent users means a company will invest resources into underperforming ads, while never putting any spend behind the ads that scored the best with real consumers.
This was just a limited study of a particular campaign. As we expand our research, we expect to find similar results. While including fraudulent users may end up not changing the results of some campaigns, is that a risk you want to take? Or is it a better strategy to know for sure that the answers you’re getting are legitimate and authentic? That way, you can confidently allocate spend on the creative you know scored best with actual humans.
How Face Verification Will Impact Your Daily Life
We believe that data quality is the central pillar of the consumer data ecosystem and surveys.
How Does Facial Verification Actually Work?
At its core, facial verification is a simple concept: it confirms you are who you say you are by analyzing your face. Think of it as a high-tech, biometric password that you can’t forget or lose. Unlike facial recognition, which tries to identify a person in a crowd by matching their face against a large database (a one-to-many comparison), verification performs a one-to-one check. It compares your live face to a stored, trusted image, like the one on your driver’s license or a selfie you provided during enrollment, to answer a single question: “Is this the same person?” This distinction is key, as verification is focused on securing an individual’s account or access, not on broad surveillance.
The Technical Process: From Face to Code
When you use your face to unlock a service, the system isn’t just saving a picture of you. Instead, it performs a sophisticated analysis. As platforms like Meta explain, the process starts when you provide a video selfie or a photo. The technology then maps the unique features of your face—like the distance between your eyes, the shape of your nose, and the contour of your jawline. These measurements are converted into a unique numerical code, often called an “embedding” or a biometric template. This code is a mathematical representation of your face, making it incredibly difficult to reverse-engineer back into an image. It’s this code, not your photo, that gets compared during future verification checks.
The Role of Human Review
While automated systems are incredibly fast and accurate, they aren’t infallible. What happens when a verification attempt is ambiguous? Maybe the lighting is poor, the camera angle is odd, or the user has a new pair of glasses. In these edge cases, some high-stakes verification processes incorporate a human review step. A trained specialist can examine the verification attempt to make a final determination, adding a layer of common sense and nuance that algorithms might miss. This human-in-the-loop approach ensures fairness and accuracy, preventing legitimate users from being locked out while still catching sophisticated fraud attempts. It’s a practical way to balance the efficiency of AI with the reliability of human judgment.
User Consent and Data Privacy
Trust is the foundation of any biometric system. Users need to feel confident that their most personal data is being handled responsibly. That’s why leading platforms build their verification processes around explicit user consent. You must give your permission each time the technology is used to confirm your identity. Furthermore, privacy-centric design dictates that your biometric data is treated as temporary. The numerical “embeddings” created from your selfie are typically used only for the immediate comparison. Reputable systems delete this data as soon as the check is complete, whether a match was found or not. This prevents the creation of permanent databases of facial templates, significantly reducing the risk of data breaches and misuse.
Legal Classification of Facial Data
Regulators around the world recognize the sensitive nature of the data that makes you, you. Under legal frameworks like Europe’s GDPR and California’s CCPA, biometric data—including facial templates—is classified as a special category of personal information. This designation means it requires the highest level of protection. Companies that handle this data must adhere to strict rules regarding its collection, processing, and storage. They need a clear legal basis for using it, must implement robust security measures to protect it, and are obligated to be transparent with users about how their information is being handled. This legal scaffolding provides essential safeguards, holding companies accountable and giving users greater control over their personal identity.
Common Uses and Applications of Facial Verification
Facial verification has quietly moved from the realm of science fiction into our daily routines. Its applications are expanding rapidly because it solves a fundamental challenge: proving identity quickly and securely without adding unnecessary friction. While many of us first encountered it on our smartphones, the technology is now being deployed across a wide range of industries to protect accounts, streamline processes, and build trust in digital interactions. From securing financial transactions to speeding up travel, facial verification is becoming an invisible but essential part of modern life, offering a more intuitive and personal way to interact with the services we rely on every day.
Security for Devices and Transactions
The most familiar use of facial verification is likely in your pocket. Technologies like Apple’s Face ID and similar systems on Android devices have replaced PINs and passwords for millions of users. This application extends far beyond just unlocking your phone. It’s used to authorize payments through mobile wallets, log in to sensitive applications like banking and healthcare portals, and confirm purchases in app stores. By linking your identity directly to your device, it creates a powerful, no-contact security measure. As security experts at Kaspersky note, it’s a seamless way to keep your digital life safe, turning your face into the key for your most important accounts and transactions.
Law Enforcement and Border Control
On a larger scale, government agencies use facial verification to enhance public safety and manage borders. At airports, automated gates use the technology to compare a traveler’s face to the image on their e-passport, speeding up immigration lines while maintaining security. Law enforcement agencies also use facial verification to confirm the identity of individuals during stops or to compare a suspect’s image against a specific mugshot database. These applications are focused on one-to-one matching to verify an identity against a provided document or a single existing record, which helps ensure accuracy and limit the scope of the search. It’s a tool used to make existing processes more efficient and reliable.
Commercial Uses in Retail and Healthcare
Businesses are finding creative ways to use facial verification to improve customer experiences. In retail, it can be used for age verification when purchasing restricted goods, offering a faster and more private alternative to showing a physical ID. Some innovative stores are even experimenting with it to enable checkout-free shopping. In healthcare, facial verification can securely identify patients upon check-in, ensuring the correct person receives the correct care and reducing the risk of insurance fraud. This not only streamlines administrative processes but also adds a critical layer of safety, preventing medical errors and protecting sensitive patient information from unauthorized access.
Aiding Social Causes Like Finding Missing Persons
Beyond security and commerce, facial verification technology plays a vital role in humanitarian efforts. Organizations dedicated to finding missing persons can use it to help identify individuals who may be unable to identify themselves, such as young children or adults suffering from memory loss. By comparing a person’s photo against databases of missing individuals, these groups can generate leads and reunite families. This powerful application highlights the technology’s potential for social good, leveraging its capabilities to protect the vulnerable and bring hope to communities affected by loss. It’s a compelling example of how technology can be used to strengthen human connections and provide aid where it’s needed most.
The Benefits of Facial Verification Technology
The rapid adoption of facial verification isn’t just about novelty; it’s driven by tangible benefits for both businesses and their users. At its heart, the technology offers a powerful combination of enhanced security and effortless convenience. It replaces fallible, traditional methods like passwords and security questions with something uniquely personal and much harder to compromise. For businesses, this means a more robust defense against fraud and a smoother customer experience. For users, it means less time spent remembering credentials and more time engaging with services securely and confidently. This win-win proposition is why facial verification is becoming a go-to solution for establishing trust online.
Improved Security and Threat Detection
The single greatest advantage of facial verification is its security. Unlike passwords that can be stolen, shared, or forgotten, your face is uniquely yours and always with you. This makes it an exceptionally strong factor for authentication. For businesses, implementing facial verification can dramatically reduce the risk of account takeover fraud, where criminals use stolen credentials to access user accounts. It also serves as a powerful deterrent against the creation of fake accounts by bots or bad actors. By ensuring that a real, unique human is behind every account, companies can protect their platforms, secure their customers’ data, and maintain the integrity of their online communities.
Convenience and Speed in Everyday Tasks
We all suffer from password fatigue. Juggling dozens of complex, unique passwords for different services is a constant source of frustration. Facial verification eliminates this friction entirely. The simple act of looking at your device is enough to grant you access, authorize a payment, or complete a check-in process. This seamless experience is not just a minor convenience; it fundamentally improves the user’s relationship with technology. Tasks that once required multiple steps of typing and remembering can now be completed in a second. This speed and simplicity encourage better security habits, as users are more likely to protect accounts when doing so is effortless.
Easy Integration for Businesses
In the past, implementing biometric security was a complex and expensive undertaking reserved for large corporations. Today, facial verification technology is far more accessible. Many providers offer solutions that can be integrated into existing websites and applications through a simple API (Application Programming Interface). This allows businesses of all sizes to add a robust layer of identity verification without needing to build the underlying technology from scratch. Solutions like Realeyes’ VerifEye are designed to be lightweight and user-friendly, enabling platforms to quickly confirm that there’s a real person behind a profile or payment, protecting their systems and decisions at scale.
Risks, Concerns, and User Resistance
Despite its clear benefits, facial verification technology is not without its challenges and controversies. The conversation around its use is filled with valid questions about privacy, accuracy, and the potential for misuse. For the technology to earn widespread, lasting trust, these concerns must be taken seriously and addressed head-on by developers, businesses, and regulators. Acknowledging the risks is the first step toward building ethical, responsible systems that protect users as effectively as they secure accounts. Ignoring these issues not only invites user resistance but also risks undermining the very trust the technology aims to build.
The Threat of Mass Surveillance and Privacy Invasion
Perhaps the most significant concern is the fear of a “Big Brother” scenario. Critics worry that the normalization of facial scanning could pave the way for mass surveillance by governments or corporations, eroding personal privacy and anonymity. As Kaspersky points out, the potential for this technology to track people’s movements and activities without their consent raises profound questions about civil liberties. This is why the distinction between one-to-one verification (confirming your identity for a specific service) and one-to-many recognition (identifying you in a crowd) is so critical. Responsible implementation focuses strictly on the former, with strong data protection and consent-based frameworks to prevent function creep.
Accuracy, Errors, and Potential Bias
No technology is perfect, and facial verification systems are no exception. Early versions of the technology showed significant biases, performing less accurately for women and people of color. While leading systems have made enormous strides in fairness and accuracy, the risk of error and bias remains a concern. A false rejection could wrongfully deny someone access to essential services, while a false acceptance could lead to a security breach. Businesses must perform due diligence when selecting a verification provider, ensuring the technology has been rigorously tested across diverse demographic groups to ensure it performs accurately and equitably for all users.
The Challenge of Securing Biometric Data
Your face is the ultimate personal data. If a database of passwords is stolen, you can change them. If a database of facial templates is breached, the consequences are permanent. This makes securing biometric data a high-stakes responsibility. A breach could expose users to sophisticated forms of identity theft that are incredibly difficult to recover from. That’s why best practices in the industry, such as converting faces to numerical codes and deleting them immediately after a check, are so important. Companies implementing facial verification must invest in state-of-the-art security to protect this sensitive information, as the cost of failure is unacceptably high.
Why Some Users Try to Bypass Verification
When a user tries to trick a facial verification system, it isn’t always for malicious reasons. While some are fraudsters attempting to create fake accounts or take over existing ones, others might be privacy-conscious individuals trying to use a service without revealing their identity. Some users may also attempt to create multiple accounts to take advantage of promotions or to manage different online personas. Understanding these motivations is key to building better systems. The goal isn’t just to block bad actors but to build a system that is trustworthy and transparent, encouraging legitimate users to participate honestly while effectively filtering out those who pose a genuine threat.
Technical Hurdles for Implementation
Deploying a facial verification system that works reliably in the real world is a significant technical challenge. The system must be able to function across a huge variety of devices, from high-end smartphones to low-resolution webcams. It needs to account for countless environmental variables, including poor lighting, awkward camera angles, and partially obscured faces (e.g., from hats or glasses). Furthermore, it must be sophisticated enough to defend against “spoofing” attacks, where a fraudster might try to use a photo, video, or mask to fool the system. Overcoming these hurdles requires advanced AI and machine learning models that are robust, flexible, and constantly evolving to stay ahead of new threats.
Facial Verification by the Numbers
To understand the true impact of facial verification, it helps to look at the data behind its growth. This isn’t a niche or futuristic technology anymore; it has become a mainstream tool integrated into the digital fabric of our lives. The statistics reveal a story of widespread adoption and rapidly improving performance. From social media to global travel, billions of people now interact with facial verification systems regularly. This broad acceptance is fueled by the technology’s increasing reliability, with top-tier systems now achieving accuracy rates that rival, and in some cases surpass, human capabilities.
Widespread Adoption and Usage Statistics
The scale of facial verification usage is staggering. According to research from Clearview AI, a company in the facial recognition space, more than half of the world’s population uses the technology on a regular basis. This might sound surprising, but consider the common applications. Many people use it dozens of times a day just to unlock their smartphones. It’s also the technology behind photo-tagging suggestions on social media platforms and is increasingly used at airports, stadiums, and retail stores. This widespread, often voluntary, adoption demonstrates a growing public comfort with using biometrics for convenience and security in low-risk, everyday scenarios.
Claims of System Accuracy
A primary driver of adoption is the technology’s impressive accuracy. While early systems struggled, modern AI-powered facial verification is remarkably precise. For example, Clearview AI claims its technology achieves over 99% accuracy across all demographics. Many top commercial providers report similar performance levels in their own testing. It’s important to note that real-world accuracy can be affected by factors like image quality and lighting. However, these figures show that the underlying technology has reached a point of maturity where, under proper conditions, it can perform one-to-one verification with an extremely low margin of error, making it a highly reliable tool for identity confirmation.
Frequently Asked Questions
How is facial verification different from the facial recognition I hear about in the news? That’s a great question, and the distinction is critical. Think of it this way: facial recognition is like a security guard trying to identify one person in a massive crowd by comparing their face to a huge database of photos. It’s a one-to-many search. Facial verification, on the other hand, is like a bouncer checking your ID at the door. It performs a simple one-to-one check to answer the question, “Is this person who they claim to be?” It compares your live face only to the trusted image you provided, making it a focused security tool, not a broad surveillance method.
What happens to a user’s facial data after they complete a scan? Is it stored forever? Privacy is the foundation of this technology, so your data isn’t kept in a permanent gallery. When a user completes a verification scan, the system maps their unique facial features and converts them into a numerical code, or template. This code is used for the immediate, one-time comparison. Reputable systems, including ours, are designed to delete this biometric template as soon as the check is complete. The goal is to confirm a real human is present, not to build a database of faces.
We already use tools like CAPTCHA to filter bots. Why do we need something more? While CAPTCHA was a good first line of defense, today’s bots are far more sophisticated and can often solve those puzzles easily. CAPTCHA primarily checks if a user can follow instructions, not if they are a real, unique human. Facial verification provides a much stronger layer of proof. It confirms that a living, distinct person is behind the screen, effectively filtering out not just simple bots but also click farms and individuals using multiple fake profiles to skew your data.
Will adding a face scan create a frustrating experience for my users? This is a common concern, but modern verification is designed to be incredibly fast and seamless. The process usually takes just a couple of seconds and is as simple as taking a selfie. When you compare that to the frustration of forgotten passwords or trying to decipher blurry letters in a CAPTCHA, it’s often a much smoother experience. The key is to offer a process that feels secure and effortless, which ultimately builds more trust than asking users to jump through outdated hoops.
Can bad data from bots and fake users really impact my business strategy that much? Absolutely. Imagine you’re testing two different ads to see which one resonates more with your target audience. Our research showed that when fraudulent data was included, the results pointed to the wrong ad as the winner. A company acting on that flawed insight would invest its marketing budget into an underperforming campaign. By ensuring your feedback comes only from real, verified people, you can be confident that your strategic decisions—from product development to ad creative—are based on genuine human truth, not automated noise.
Key Takeaways
- Protect Your Strategy from Flawed Data: Bots and fraudulent users can corrupt your market research, leading to costly mistakes. Face verification ensures your insights are based on real human feedback, allowing you to confidently build products and campaigns for an actual audience.
- Understand the Verification vs. Recognition Difference: Facial verification is not surveillance; it’s a simple one-to-one check to confirm a user is who they claim to be. Ethical systems require user consent and use temporary data, protecting privacy while securing your platform.
- Improve Security and the User Experience Simultaneously: You don’t have to choose between robust security and a smooth customer journey. Face verification replaces insecure, frustrating passwords with a seamless process that reduces fraud and keeps legitimate users engaged.
Related Articles
- Panels are Failing to Combat Fraud Effectively – Realeyes
- How Face Verification Will Save Advertisers Billions in Flawed Spend – Realeyes
- Your Guide to Preventing Synthetic Identity Fraud
- VerifEye Demo: Revolutionizing Survey Quality with Responsible AI – Realeyes
- KYC ID Verification: A Complete Guide for 2025
