Building a great platform means protecting it from bots, fraudsters, and fake accounts. These bad actors can quickly erode trust and ruin the experience for your real users. A user verification API is your digital gatekeeper, but choosing the right one is key. The real question is, which APIs offer fraud detection along with user identity verification? Some tools just confirm a person is real, while others provide deeper security. This guide will help you find reliable tools for user verification, so you can create a safer environment without frustrating the people who depend on your service.
Key Takeaways
- Verification Builds Your Foundation of Trust: An API is more than a security tool—it’s essential for preventing fraud, building user confidence, and meeting critical compliance standards like GDPR and HIPAA.
- Select an API That Aligns with Your Goals: Look for a partner that offers clear documentation for your developers, flexible verification channels for your users, and the proven ability to scale as your platform grows.
- Prioritize a Seamless User Experience: The biggest challenge is balancing security with convenience. Choose a precise API and test your implementation thoroughly to stop bad actors without frustrating your legitimate customers.
What Exactly Is a User Verification API?
Think of a user verification API as a digital bouncer for your app. It’s a specialized tool that helps your business confirm that the person signing up, logging in, or making a transaction is exactly who they claim to be. Instead of building a complex and expensive identity-checking system from scratch, you can integrate an API that handles the heavy lifting for you. This service acts as a bridge between your application and a verification provider, allowing you to tap into their established technology to protect your platform and your users.
At its core, a user verification API is all about establishing trust. It provides a way to check that a user is a real person, which is fundamental for preventing fraud, securing accounts, and maintaining the integrity of your online community. Whether it’s confirming a phone number, validating an email address, or using more advanced biometric checks, these APIs give you the tools to create a safer environment. This is especially important for platforms where financial transactions occur or sensitive personal data is stored. By implementing a verification system, you send a clear message that you prioritize security and are committed to protecting your users from bad actors.
How Does the Verification Process Actually Work?
The process behind a user verification API is designed to be both secure and straightforward for the user. It typically starts when a user performs a specific action, like creating an account or resetting a password. Your app then makes a call to the verification API, which kicks off the identity-checking workflow. A common method involves sending a unique, temporary code to the user through a channel they own, such as an SMS message, email, or a push notification from an authenticator app.
Once the user receives the code, they enter it into your app to complete the check. The API then confirms if the code is correct and sends a success or failure message back to your application. More sophisticated APIs can add extra layers of security, like asking a user to take a live photo while holding a handwritten note with a specific code. The API then analyzes the image to ensure the note matches and that the person is physically present, effectively stopping bots in their tracks. This entire exchange happens in seconds, creating a secure but low-friction experience.
What Makes a User Verification API Tick?
A robust user verification API is made up of several key components working together behind the scenes. First, there’s the infrastructure that manages connections to global communication networks, like phone carriers for sending SMS codes. The API provider handles all the complexities of these connections so you don’t have to. Another critical piece is the logic for generating secure, single-use codes and monitoring for fraudulent activity, such as repeated verification attempts from the same device.
On top of that, strong security and compliance features are essential. A quality API will include tools for secure authentication, data encryption, and access logging to protect sensitive user information. For businesses in regulated industries like healthcare or finance, the API must also align with standards like HIPAA or financial data protection laws. These built-in components ensure that the verification process is not only effective but also meets critical API compliance and security requirements, giving you peace of mind.
API vs. SDK: What’s the Difference?
When you start exploring verification solutions, you’ll quickly run into two acronyms: API and SDK. While they’re often mentioned together, they play very different roles. An API, or Application Programming Interface, is the engine that does the work. It’s a set of rules that allows your application to communicate with the verification provider’s service. When your app needs to verify a user, it sends a request to the API, which processes the information, performs the check, and sends a result back. The API is the core functionality that confirms a user’s identity.
An SDK, or Software Development Kit, is the toolkit that makes the engine easier to use. It’s a package of pre-written code, tools, and documentation that your developers can use to integrate the API into your app more quickly. Instead of writing every line of code from scratch to connect to the API, an SDK provides the necessary building blocks. A good verification partner will offer a robust API for flexibility and a user-friendly SDK to streamline the development process, helping you get your security features up and running with less effort.
Beyond the Individual: KYC vs. KYB
As you build out your platform’s safety measures, it’s important to know who you need to verify. This is where the distinction between KYC and KYB comes in. KYC, or Know Your Customer, is the process of verifying the identity of an individual user. This typically involves checking government-issued IDs, using biometric data like a selfie, and confirming personal information. KYC is essential for B2C platforms, financial services, and any business that needs to prevent individual fraud and comply with anti-money laundering (AML) regulations.
On the other hand, KYB, or Know Your Business, focuses on verifying an entire business entity. This process is more complex, as it involves validating a company’s registration, identifying its beneficial owners, and ensuring it’s a legitimate operation. KYB is critical for B2B marketplaces, payment processors, and platforms that onboard corporate clients. Whether you’re dealing with an individual or a business, the process must be protected against bots and deepfakes. Ensuring a real human is present during onboarding is the first step in building a secure foundation for both KYB and KYC.
Why Your App Needs a User Verification API
Integrating a user verification API isn’t just about adding another security layer; it’s a strategic move that impacts everything from user trust to your bottom line. In a digital world where bots and fake accounts are increasingly sophisticated, proving that a real person is behind the screen has become essential. It’s the foundation for creating a safe, reliable, and valuable platform. When you can confidently verify your users, you protect your business from fraud, create a better experience for legitimate customers, and build a community that people actually want to be a part of.
Think of it as the digital equivalent of a firm handshake. It establishes a baseline of trust that allows for more meaningful and secure interactions online. Whether you’re processing payments, hosting a social platform, or providing a critical service, knowing your users are who they say they are is no longer a nice-to-have—it’s a necessity. A user verification API handles this complex process for you, often seamlessly in the background, allowing you to focus on your core product. By implementing one, you ensure your platform remains a secure and trustworthy environment. It’s a proactive step that strengthens your app from the inside out, safeguarding both your users and your brand’s reputation in the long run.
Stop Fraud in Its Tracks and Secure Your Platform
At its core, user verification is your first line of defense against bad actors. It’s designed to stop fraudulent activities like identity theft and account takeovers before they can harm your users or your business. By confirming that the person signing up or logging in is a real, unique individual, you can effectively filter out bots and malicious users trying to exploit your system. This is especially critical for platforms that handle sensitive data or financial transactions. A strong verification process ensures that the information provided is authentic, protecting your entire ecosystem from security risks and building a safer space for everyone.
The Scale of the Problem: Fraud by the Numbers
The threat of online fraud isn’t just a hypothetical risk; it’s a widespread and costly reality. While it’s tempting to think a one-time check at sign-up is sufficient, the data tells a different story: about two-thirds of fraud isn’t detected until a transaction occurs. This means bad actors are already inside your system, often waiting to strike during off-peak hours. In fact, a significant number of fraudulent transactions happen late at night. This problem is so pervasive that the market for AI-powered fraud detection is expected to reach nearly $11 billion. These aren’t just abstract numbers; they represent real threats that can compromise data, drain resources, and fundamentally undermine the trust you’ve worked so hard to build with your community.
Create a Seamless and Secure User Experience
Security measures often feel like they come at the expense of a smooth user experience, but that’s not the case with modern verification APIs. The best solutions are designed to be as frictionless as possible, often working quietly in the background. By quickly and accurately verifying users upfront, you can reduce the need for cumbersome security challenges later on. This seamless process helps build confidence from the very first interaction. When users feel that their accounts are secure without having to jump through hoops, they are more likely to engage with your app and trust your platform with their information.
Earn User Trust While Staying Compliant
Trust is the currency of the digital world, and verification is how you earn it. When users know your platform is populated by real people, the quality of interactions improves, and a genuine community can flourish. Beyond building user confidence, a verification API is also a key tool for meeting regulatory requirements. For industries like healthcare and finance, adhering to standards like HIPAA and GDPR is non-negotiable. Implementing a compliant verification process demonstrates your commitment to protecting user data, which is fundamental to maintaining trust and showing you handle sensitive information ethically and responsibly.
What Features Should Your User Verification API Have?
When you’re ready to choose a user verification API, it’s easy to get overwhelmed by the options. They all promise to secure your platform, but the right solution does more than just put up a gate—it creates a seamless, trustworthy experience for your genuine users. To find the best fit, you need to look past the marketing claims and focus on the core features that will actually support your business goals. Think about how you want to interact with your users, the level of security you need, how much work your development team can take on, and your plans for future growth. These factors will guide you to the API that truly works for you.
Flexible Channels to Reach Users on Any Platform
Your users are everywhere, so your verification methods should be too. A top-tier API provides multiple ways to confirm a user’s identity, meeting them on the channels they already use. This could mean sending a one-time password (OTP) via SMS, email, or even a push notification through an app. For example, some APIs let you send verification codes through WhatsApp, which is essential for reaching a global audience. Offering this kind of flexibility isn’t just about convenience; it’s about creating a smoother onboarding process. When users can choose their preferred method, they’re more likely to complete the verification step, reducing drop-off and getting them into your app faster.
APIs That Offer Fraud Detection and Identity Verification
In an era of deepfakes and sophisticated bots, a simple password or OTP isn’t always enough. That’s why leading verification APIs incorporate real-time fraud detection and biometric checks. This goes beyond what a user knows (a password) and verifies who they are. These systems can use a device’s camera to perform a liveness check, ensuring the person is physically present and not just a photo or video. Some advanced APIs even compare a live selfie against a government-issued ID to confirm a match. These instant, intelligent checks are your front line of defense, stopping automated attacks and identity fraud before they can compromise your platform and your community.
Targeting Specific Threats: Types of Fraud Detection
Not all fraud is created equal, and a one-size-fits-all security approach just doesn’t cut it. Different threats emerge at different points in the user journey, from the moment someone creates an account to the everyday transactions they make. A smart verification strategy recognizes this and deploys specific tools to address each vulnerability. By understanding the distinct types of fraud, you can choose an API that provides targeted protection where you need it most. This ensures you’re not just building a wall, but a sophisticated defense system that adapts to the tactics of modern bad actors.
Identity and Onboarding Fraud
The first point of entry is often the most vulnerable. Identity and onboarding fraud happens when a bad actor attempts to create an account using stolen or entirely fabricated information. This is the classic “fake account” problem, and it can lead to everything from spam to large-scale financial crime. To combat this, modern APIs often combine identity verification with other data points. For example, a lending platform might use an API that checks a government ID and simultaneously pulls a credit score. This integrated approach, as noted by CRS Credit API, streamlines the onboarding process for legitimate customers while making it significantly harder for fraudsters to slip through the cracks.
Transaction and Payment Fraud
Securing the front door is only half the battle. Many fraudulent activities occur long after an account has been created. Transaction fraud involves bad actors using compromised accounts or stolen payment information to make unauthorized purchases. According to industry analysis, about two-thirds of fraud isn’t caught at sign-up but during later transactions, which underscores the need for continuous, real-time monitoring. A simple login isn’t enough; your system needs to be able to spot suspicious behavior as it happens. This is where verification APIs that offer ongoing risk assessment become invaluable, protecting both your business and your users from financial loss.
Account Takeover Prevention
An account takeover is one of the most damaging forms of fraud, where a malicious actor gains unauthorized access to a legitimate user’s account. This is often accomplished through phishing scams or by using credentials stolen from other data breaches. The goal is to exploit the trust and history associated with the existing account. The most effective way to prevent this is to ensure the person logging in is the actual account owner. By confirming that the user is a real, unique individual at critical moments, you can effectively filter out bots and unauthorized users trying to hijack an account, protecting your customers’ data and preserving the integrity of your platform.
Advanced Security: The Role of Liveness Detection
As fraudsters get smarter, basic verification methods can fall short. It’s one thing to confirm a user has a phone number, but it’s another to prove they are a real person who is physically present. This is where liveness detection comes in. It’s a form of biometric verification that uses a device’s camera to determine if a user is a live human being, not just a photo, a video, or a sophisticated deepfake. As Vouched highlights, liveness detection is a crucial security step for preventing fake accounts and stopping account takeovers. It adds a powerful layer of security that can differentiate between a genuine user and a digital impersonation, which is essential for building true trust online.
Active vs. Passive Liveness Checks
Liveness detection generally comes in two flavors: active and passive. Active liveness requires the user to perform a specific action, like smiling, blinking, or turning their head. While effective, this approach adds a step to the user’s journey and can sometimes feel clunky. In contrast, passive liveness works silently in the background without asking the user to do anything. It analyzes a single, natural image or a short video clip to confirm human presence, offering a completely frictionless experience. This passive approach is ideal for platforms that want to maintain a high level of security without disrupting the user flow, quietly confirming a real person is present while keeping the interaction feeling natural and human.
A Smooth Setup: Easy Integration and Clear Documentation
The most powerful API in the world won’t do you any good if your developers can’t figure out how to implement it. A great user verification API should be designed for a smooth integration process, backed by clear, comprehensive documentation. Look for providers that offer detailed guides, code samples, and software development kits (SDKs) for various programming languages. This kind of support is a game-changer, as it drastically cuts down on development time and headaches. When your team can easily add the API to your existing systems, you can get your security measures up and running quickly and focus on building your core product.
Can It Grow with Your User Base?
Your verification solution needs to be able to handle your traffic on day one and on day one thousand. As your user base grows, your API must scale effortlessly without any drop in performance. A reliable API can process millions—or even billions—of verifications without breaking a sweat, ensuring a consistently fast experience for every user, no matter where they are in the world. This requires a global infrastructure that can handle high volume and navigate different regional carrier rules. When you’re evaluating options, ask about uptime guarantees and performance metrics. Your verification process is a critical part of your user journey, and it needs to be as dependable and scalable as the rest of your platform.
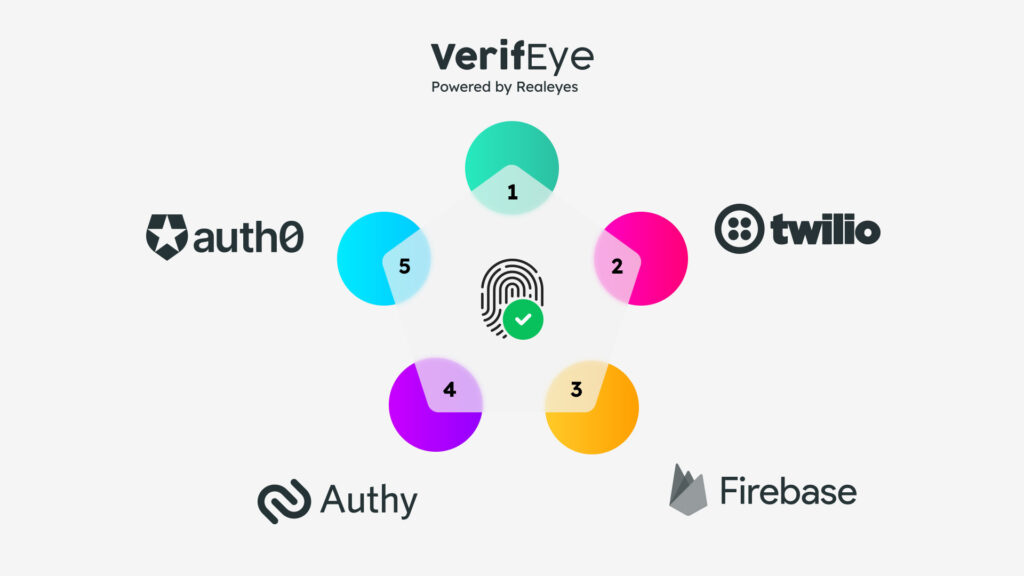
Which User Verification Tools Are Most Reliable?
Choosing the right API depends entirely on your app’s specific needs, from the level of security required to the user experience you want to create. Some APIs offer simple SMS codes, while others provide sophisticated biometric checks. To help you find the perfect fit, let’s walk through five of the best user verification APIs available. Each one brings something different to the table, whether it’s a focus on privacy, developer-friendliness, or an all-in-one identity solution.
Realeyes VerifEye: For Human-Centered Verification
If your goal is to confirm you’re interacting with a real, unique human without collecting sensitive personal data, Realeyes is in a class of its own. Instead of verifying who someone is, its VerifEye technology confirms that they are a live person. It uses a quick, anonymous facial scan to validate personhood in seconds. This process is incredibly lightweight, which means less friction for your users during critical moments like registration or checkout.
What really sets it apart is its privacy-first design. The system operates under a GDPR-compliant consent framework, so you can detect bots and prevent duplicate accounts while respecting user privacy. It’s a cost-effective way to ensure data integrity, especially for platforms that rely on genuine human interaction, like research panels or online communities. You can see a quick demo to understand just how seamless it is.
Twilio Verify: A Developer Favorite
Twilio is a giant in the communications API space, and its Verify API is a trusted, straightforward solution for multi-factor authentication (MFA). It lets you send one-time passcodes (OTPs) to users through various channels, including SMS, voice calls, email, and push notifications. This flexibility allows you to meet your users where they are, offering verification methods they’re already comfortable with.
The Twilio Verify API is a favorite among developers for its clear documentation and ease of integration. If you need a reliable way to implement 2FA for logins, transactions, or password resets, Twilio provides a robust and scalable tool. It’s less about confirming a person’s identity from scratch and more about securing an existing account by adding another layer of protection.
Auth0: Comprehensive Identity Solutions
Think of Auth0 as more than just a verification tool; it’s a complete identity platform. If your application requires a comprehensive solution for authentication and authorization, Auth0 has you covered. It handles everything from simple email and password logins to complex enterprise features like Single Sign-On (SSO) and social logins with providers like Google, Facebook, and Apple.
Verification is a core part of its multi-factor authentication capabilities. Auth0 allows you to easily configure rules that trigger MFA based on risk factors, such as a login from a new device or location. It’s an excellent choice for businesses that want a powerful, all-in-one system to manage user identities securely without having to build everything from the ground up.
Firebase Authentication: The Go-To for Google Apps
For developers building on Google’s ecosystem, Firebase Authentication is often the natural choice. It’s designed to get you up and running quickly with secure user sign-in for your web or mobile app. The service provides backend services, easy-to-use SDKs, and ready-made UI libraries to authenticate users. It supports a wide range of methods, including email and password, phone number verification, and federated identity providers.
One of the biggest draws of Firebase Authentication is its tight integration with other Firebase services, like its databases and cloud functions. It also has a generous free tier, making it an accessible option for startups and independent developers who need a reliable authentication solution without a significant upfront investment.
Authy: Focused on Strong 2FA
While also a Twilio product, the Authy API serves a more specific purpose: providing best-in-class push authentication and soft-token OTPs. Instead of just sending a simple SMS code, Authy lets you embed a more secure and user-friendly MFA experience directly into your application. Users can approve or deny login requests with a single tap from their trusted device via the Authy app or a custom-branded push notification.
The Authy API is ideal for applications that handle sensitive data, like financial or healthcare platforms, where SMS-based 2FA might not be secure enough. It gives you the tools to build a modern, frictionless authentication flow that protects against phishing and other account takeover attacks.
Microblink: For ID-Focused Verification
When your verification process needs to confirm a user’s legal identity, Microblink is a powerful choice. It’s designed for high-stakes industries like fintech, digital banking, and crypto, where meeting compliance standards like Know Your Customer (KYC) is essential. The API specializes in stopping identity fraud by scanning government-issued IDs and using facial scans to ensure the person holding the ID is real and physically present. It’s particularly effective at detecting sophisticated fakes, including manipulated images and deepfake videos, giving you a high degree of confidence that your users are who they claim to be.
Plaid: For Financial Data Verification
For applications in lending or financial services, verifying a user’s identity is often tied to their financial health. Plaid offers a unique approach by connecting directly to an applicant’s bank account. With user permission, it can instantly check income, spending habits, and account ownership in real time. This method provides a clear and current picture of a user’s financial situation, which is invaluable for making credit decisions. It’s especially useful for evaluating individuals who may have a limited credit history, allowing you to assess risk based on actual financial behavior rather than just a traditional credit score.
LexisNexis Risk Solutions: For Deep Public Record Checks
Sometimes, a simple ID check isn’t enough. For situations requiring a deeper level of assurance, LexisNexis Risk Solutions provides one of the most comprehensive verification services available. It goes beyond a single document by cross-referencing a user’s information against a massive database of public records, including utility bills, property ownership, and government data. This multi-layered approach allows it to build a highly accurate identity profile and uncover complex fraud schemes, such as synthetic identities or organized fraud rings. It’s the go-to solution for organizations that need to make high-confidence decisions and mitigate significant risks.
SEON: For Behavioral and Device Analytics
SEON takes a modern, digital-first approach to fraud detection by focusing on a user’s behavior and digital footprint. Instead of relying on identity documents, it analyzes hundreds of data points in real time, such as a user’s device, IP address, and email address. By examining this digital footprint, SEON can spot suspicious patterns that often indicate fraud, like the use of a virtual machine or a disposable email address. Its flexible, low-code tools make it a great fit for online businesses, particularly digital lenders, that need a fast and frictionless way to assess risk without adding friction to the user experience.
Riskified: For E-commerce Chargeback Guarantees
For e-commerce platforms, the biggest fraud-related headache is often chargebacks. Riskified tackles this problem head-on with a unique “chargeback guarantee” model. The platform uses sophisticated machine learning to analyze every transaction and decide whether to approve or decline it. If Riskified approves a sale that later turns out to be fraudulent, it covers the entire cost of the chargeback. This shifts the financial risk from the merchant to Riskified, allowing online stores to confidently accept more orders without worrying about potential fraud losses. It’s an ideal solution for retailers focused on protecting their revenue and streamlining their payment process.
How to Overcome Common Implementation Hurdles
Integrating a user verification API is a smart move, but it’s not always a simple plug-and-play process. Like any new technology, it comes with its own set of potential hurdles. Being aware of these common challenges ahead of time can help you plan a smoother rollout and choose a partner who can help you clear them successfully. From keeping your users happy to navigating complex technical requirements, here’s what you should prepare for as you get started.
Finding the Sweet Spot Between Security and UX
One of the biggest challenges is finding the sweet spot between robust security and a frictionless user experience. If your verification process is too complicated or demanding, you risk frustrating legitimate users and causing them to abandon your app. On the other hand, a process that’s too simple might not offer enough protection against fraud. The goal is to implement a system that is strong enough to stop bad actors but seamless enough that your real users barely notice it. This balance is essential, as overly stringent security can lead to significant user drop-off, while weak measures leave you vulnerable.
What to Do When Integrations Get Complicated
Connecting a new API to your existing tech stack can be tricky. Even with a well-designed API, you might run into issues with inconsistent data formats, unclear documentation, or unexpected security conflicts. To get ahead of this, your development team should prioritize solutions with clear specifications and comprehensive guides. Proper error handling and thorough testing are non-negotiable steps to ensure the verification API works seamlessly with your application. Taking the time to address these potential API integration challenges from the start will save you countless headaches down the road.
How to Minimize False Positives and User Frustration
An effective verification system needs to be accurate. When the system incorrectly flags a real user as a threat (a false positive) or fails to catch an actual fraudster (a false negative), it creates problems. False positives are particularly damaging because they block legitimate customers and can seriously damage their trust in your platform. High rates of these errors create unnecessary friction and can drive people away for good. It’s vital to choose a verification API that is finely tuned to minimize these occurrences and can distinguish between genuine human behavior and sophisticated threats with high precision.
Planning for Failure: Creating User-Friendly Fallbacks
No matter how sophisticated your verification API is, there will be times when it doesn’t work as expected. A camera might be blurry, a network connection might drop, or the system might simply make a mistake. When a legitimate user fails a verification check, it can feel like a dead end—or worse, an accusation. Without a clear path forward, that user is likely to get frustrated and leave. This is why planning for these moments is so critical. A good fallback plan isn’t just about error handling; it’s about preserving the user’s trust and giving them a way to prove they’re real, even when technology stumbles.
So, what does a user-friendly fallback look like? Instead of showing a generic “Verification Failed” message, guide the user to another option. If a liveness check fails, you could offer to send a one-time code to their registered email or phone number. For more sensitive applications, you might direct them to a brief, manual review process where a support agent can assist. The key is to provide a clear, alternative route that still maintains security but doesn’t abandon the user. By designing these thoughtful recovery paths, you show users that you value their business and are prepared to help them succeed, turning a moment of potential frustration into an opportunity to build confidence.
Keeping Up with Data Privacy and Compliance Rules
When you verify users, you’re handling sensitive personal information. That means you have to be diligent about data privacy and adhere to a growing list of regulations like GDPR. Depending on your industry, you may also face specific rules, such as the need to align with HIPAA in healthcare to protect patient data. Your chosen API provider should not only be compliant themselves but also provide the tools you need to meet your own obligations. This includes features like secure data handling, encryption, and clear privacy policies that help you maintain user trust and avoid costly penalties.
Who Benefits Most from User Verification?
While just about any online platform can gain from confirming its users are real, some industries face a much higher risk from fake accounts and fraudulent activity. For these sectors, robust user verification isn’t just a nice-to-have feature; it’s a fundamental part of their business strategy. When your operations involve high-value transactions, sensitive personal data, or community trust, proving that a real person is behind the screen becomes absolutely critical.
From finance to healthcare, the need to establish digital trust is reshaping how companies interact with their customers. In banking, it’s about securing transactions and meeting strict regulatory demands. For e-commerce, it’s about preventing costly fraud and protecting customer accounts from takeovers. In healthcare, the focus is on safeguarding private patient information, especially with the growth of telemedicine. And for social platforms, it’s about preserving the integrity of the community and stopping the spread of bots and misinformation. Each of these industries leverages user verification to solve unique, high-stakes challenges, ensuring their platforms remain safe, compliant, and trustworthy for everyone involved.
Why FinTech and Banking Rely on It
In the world of finance, security and trust are everything. Financial institutions are prime targets for fraud, making user verification a critical line of defense. Implementing a verification API is essential for any organization needing a reliable way to confirm user identities, especially during onboarding and for high-risk transactions. This process is key to complying with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations. By verifying users, banks and fintech companies can confidently prevent identity theft, secure accounts, and build a foundation of trust with their customers, all while creating a smoother, faster sign-up process.
Integrating Identity Verification with Credit Scoring
For lenders, the onboarding process is a balancing act between speed and security. Combining identity verification with credit scoring through a single API is a smart way to streamline this process. Instead of juggling multiple tools, lenders can use one connection to confirm a person’s identity and pull their credit data simultaneously. This integrated approach allows for faster, more intelligent lending decisions, which is a huge advantage in a competitive market. It creates a much smoother workflow for your team and a better experience for the applicant. By confirming both identity and creditworthiness in one step, you can quickly filter out fraudulent applications and focus on the genuine customers you want to serve.
The Power of Collaboration in Fraud Prevention
In the ongoing fight against fraud, no single tool is a silver bullet. The most effective defense is a collaborative one, where different technologies work together. Lenders and other financial businesses need a strong set of fraud prevention tools that use artificial intelligence and real-time monitoring to spot risks without disrupting legitimate customers. The best systems are designed to work seamlessly with identity verification, creating a robust, multi-layered defense. By integrating these technologies, you not only strengthen your security but also improve the overall user experience. A well-designed system ensures that real users can move through your platform without unnecessary friction, while bad actors are stopped before they can cause any harm.
Securing Transactions in E-commerce
For online retailers, user verification is a powerful tool against a constant barrage of fraudulent activities. As one expert notes, it’s a “growing imperative for businesses to accurately identify and confirm authenticity… and prevent identity theft, account takeover, or fraudulent activities.” By confirming a user’s identity at sign-up or checkout, you can significantly reduce instances of payment fraud, fake reviews, and account takeovers. This not only protects your revenue but also builds customer confidence. When shoppers know their accounts and payment information are secure, they are more likely to make purchases and become loyal, repeat customers.
Protecting Patient Data in Healthcare
Patient privacy is non-negotiable in healthcare. With the rise of digital health records and telemedicine, securely verifying the identities of both patients and providers is more important than ever. Healthcare APIs must adhere to strict regulations like HIPAA to ensure patient data is protected. User verification technology provides a crucial layer of security, confirming that only authorized individuals can access sensitive medical information, book appointments, or receive virtual care. This protects patient confidentiality, prevents medical fraud, and ensures that telehealth services are delivered securely and effectively.
Building Safer Online Communities
The health of an online community depends on the authenticity of its members. Social media and content platforms are constantly battling bots, spam accounts, and coordinated misinformation campaigns that can erode user trust. Implementing user verification helps maintain the integrity of the platform by ensuring that interactions come from real people. This simple step can drastically reduce the spread of harmful content, cut down on spam, and protect users from scams and harassment. For platforms that rely on engagement metrics, verifying users also ensures that likes, shares, and comments reflect genuine human interest, providing more accurate data for creators and advertisers.
How Much Does a User Verification API Cost?
When you start looking into user verification APIs, you’ll quickly notice that there’s no single price tag. The cost can vary quite a bit, depending on the provider, the features you need, and how many users you plan to verify. Think of it less like buying a product off the shelf and more like choosing a service plan that fits your app’s specific needs. Understanding the common pricing structures and the factors that influence the final cost will help you budget effectively and find a solution that provides real value without any surprises.
Pay-Per-Use vs. Subscription Models
The most common approach you’ll see is a pay-as-you-go model, where you’re charged per verification. This cost can range from a few cents to a couple of dollars per check. For example, Twilio Verify charges a small fee for each successful verification, plus any associated fees for the channel used, like SMS or email. Many providers also offer volume-based pricing, which is great for growing platforms. With this model, the cost per verification decreases as your number of users scales up. This allows you to manage expenses predictably as your app gains more traction, ensuring your security measures can grow right alongside your user base.
Exploring Other Pricing Structures: Free Trials and Subscriptions
Beyond paying for each individual check, many providers offer subscription plans. This model is often a better fit for platforms with high or consistent verification volume, as it provides a predictable monthly cost. Instead of tracking thousands of tiny transactions, you pay a flat rate for a set number of verifications. Some services, like Vouched, note this approach is ideal for established businesses that can forecast their usage. A subscription can also come with added perks like dedicated support, making it a valuable option as you scale.
Before you commit, look for providers that offer a free trial. This is your chance to see how the API performs in your environment. A trial lets your team evaluate the documentation, test the integration, and see how the verification flow feels to a user. It’s the best way to confirm that the service is powerful and easy to work with. This hands-on experience is invaluable for making sure you’re choosing a long-term partner, not just a temporary fix for your security needs.
What Influences the Final Cost?
The base price per verification is just the starting point. Several key factors will shape your final bill. The sheer volume of verifications is the most obvious one—the more you run, the lower your per-unit cost will likely be. Another major factor is the verification channel you choose. Sending a one-time password via SMS will have a different cost than a voice call or an email. Beyond that, the complexity of the features you need plays a huge role. A simple phone verification is less expensive than a sophisticated solution that includes biometric checks or liveness detection to confirm a user is physically present. When you evaluate different vendors, be sure to consider these variables to get a clear picture of the total investment.
What Compliance Standards Do You Need to Know?
Choosing a user verification API isn’t just about features and pricing; it’s also about trust and responsibility. Handling user data means you’re subject to a web of regulations and standards designed to protect privacy and security. Getting this wrong can lead to hefty fines, legal trouble, and a serious loss of user trust. Before you commit to a provider, make sure you understand the compliance landscape and that your chosen API is built to meet these critical requirements. It’s a non-negotiable step for protecting both your users and your business.
Understanding GDPR and Global Data Protection
If you have users in Europe, the General Data Protection Regulation (GDPR) should be at the top of your mind. This regulation is all about having a “lawful basis” for processing personal data. For a user verification API, this means you need a clear, legitimate reason for collecting and handling user information. While a European hospital might process patient data based on medical necessity, using that same information for AI analytics often requires explicit consent. This is why it’s essential to ensure any API you use is built for GDPR compliance, giving you the tools to manage consent and protect user data properly.
Do You Need to Follow Industry-Specific Rules?
Beyond broad data protection laws, many industries have their own specific rules. Healthcare is a perfect example. In the United States, any API handling patient information must align with the Health Insurance Portability and Accountability Act (HIPAA). This means the service needs to support features like data encryption, secure authentication, and detailed access logging to safeguard sensitive health data. Whether you’re in finance, healthcare, or another regulated field, you need to verify that your user verification API meets the specific API compliance standards for your sector to maintain the integrity and confidentiality of your users’ information.
What Security Certifications Matter Most?
How can you quickly gauge a provider’s commitment to security? Look for certifications. Standards like ISO/IEC 27001 are a strong indicator that a company takes data security seriously. This certification shows that a provider has a robust framework for managing security risks, including controls for securing API environments. When you’re evaluating different user verification APIs, checking for relevant certifications is a smart move. It not only gives you confidence in the provider’s security practices but also strengthens the overall security of your application by building on a secure foundation.
How to Choose the Right User Verification API
Picking a user verification API is more than just a technical decision—it’s a strategic one that impacts your product, your users, and your brand’s reputation. The right API should feel like a natural extension of your team, seamlessly integrating into your workflow while providing robust security. The wrong one can lead to development nightmares, a clunky user experience, and security gaps that put everyone at risk. Before you even start looking at specific vendors, it’s helpful to create a clear framework for your evaluation.
Think about this process in three distinct phases: understanding your internal needs, vetting potential partners, and planning for a smooth rollout. This approach helps you move beyond flashy feature lists and focus on what truly matters: finding a solution that aligns with your technical infrastructure, meets your industry’s compliance standards, and delivers a secure, frictionless experience for your users. A great API partner provides more than just code; they offer clear documentation, reliable support, and a commitment to staying ahead of emerging threats. By being methodical, you can confidently select a vendor that will not only solve your immediate verification challenges but also scale with you as your platform grows and the digital landscape evolves.
First, Figure Out Your Technical Requirements
First things first, you need to look at your existing tech stack. A powerful API is useless if it doesn’t play well with your current systems. Start by mapping out your integration points and identifying any potential compatibility issues. The key here is to find an API with excellent, clear documentation that your developers can easily follow. This saves countless hours of frustration and helps prevent common implementation errors. You’ll also want to confirm that the API can handle your expected volume of verification requests without slowing down, ensuring a reliable and scalable performance as your user base grows.
What to Look For in a Vendor
Once you know what you need technically, it’s time to evaluate the vendors themselves. Look for a partner with a proven track record in security and a deep understanding of data privacy. This is especially critical if you operate in a highly regulated industry like finance or healthcare. For example, any API that handles patient information must ensure full HIPAA compliance by providing necessary safeguards like data encryption and access controls. Don’t be afraid to ask tough questions about their security protocols, certifications (like SOC 2 or ISO 27001), and how they handle data. A transparent and knowledgeable vendor will be happy to provide these details.
Map Out Your Testing and Implementation Plan
Before you commit, map out a thorough testing plan. A successful integration depends on rigorous testing to ensure everything functions correctly and provides a smooth user experience. Your plan should include both automated and manual testing to catch bugs and refine the user flow. Using automated testing tools can help you check for functionality at scale, while manual testing is crucial for evaluating the real-world user journey. Consider a phased rollout, starting with a small segment of users. This allows you to gather feedback and address any unforeseen issues before launching the integration to your entire audience, minimizing disruption and ensuring a positive reception.
### Building Your Stack: Combining Multiple Tools
Relying on a single tool to handle every aspect of user verification is like using one key to lock every door in a skyscraper—it’s just not enough. A more effective strategy is to build a security stack, layering different specialized APIs to create a comprehensive defense. For instance, many platforms find success by combining an identity fraud API with a transaction monitoring tool. You might use one service to confirm a user’s government ID during onboarding and another to analyze their behavior for suspicious patterns during a purchase. This layered approach allows you to verify different signals at different points in the user journey, creating a much stronger and more resilient system that can adapt to a wider range of threats.
### Advanced Strategies: Using a Fraud Orchestration Platform
Once you start combining multiple verification tools, managing them all can get complicated. That’s where a fraud orchestration platform comes in. Think of it as a central hub that connects and coordinates all your different security APIs. Instead of building separate, complex integrations for each tool, you plug them into the orchestration platform, which then manages the workflow. This setup allows you to easily add, remove, or swap out different verification methods as your needs change. A good fraud prevention system should be easy to integrate, quick to identify threats, and smart enough to avoid blocking real customers. An orchestration platform helps you achieve this by creating a flexible, unified system that can keep up with new fraud tactics without requiring a constant overhaul of your core code.
### Finding the Right Fit for Your Business Size
The ideal user verification strategy isn’t one-size-fits-all. A startup with a small team and limited budget has very different needs than a global enterprise managing millions of users. The right approach depends on your company’s scale, resources, and the specific risks you face. For smaller businesses, the focus is often on finding a single, high-impact solution that’s easy to implement. For larger organizations, the priority shifts to building a scalable, multi-layered system that can handle complex compliance requirements and sophisticated, high-volume attacks. Understanding where your business falls on this spectrum is the first step to choosing a solution that will protect you today and grow with you tomorrow.
Recommendations for Startups and Small Businesses
If you’re just starting out, your main goal is to get a reliable verification system in place without draining your development resources. The key is to prioritize simplicity and effectiveness. Look for an API with excellent documentation, a straightforward integration process, and responsive customer support. You need a partner who makes it easy to get up and running. Focus on solving your most critical problem first. For many, that’s simply ensuring that new sign-ups are real people, not bots. A lightweight, privacy-first solution that confirms human presence without adding a lot of friction can be a perfect starting point. As you choose an API, carefully consider how secure your data will be and how easily the tool can connect with your existing systems.
Solutions for Enterprise-Level Needs
For large-scale enterprises, the stakes are much higher, and the requirements are more complex. You need a verification stack that is not only robust but also highly scalable and compliant with global regulations. The best solutions for this level incorporate real-time monitoring and use AI and machine learning to detect emerging threats. Flexibility is also crucial; your chosen APIs must integrate seamlessly into your existing infrastructure and be able to handle massive transaction volumes without a hitch. Enterprises should look for partners that offer strong compliance frameworks, customizable workflows, and the ability to build a sophisticated, multi-layered defense that can protect against coordinated, large-scale fraud attempts.
Related Articles
- What is KYC Verification? A Complete Guide
- Third-Party ID Verification: A Complete Guide
- Why We’re Doubling Down on Human Verification – Realeyes
- Face Verification Will Revolutionize Ad Spend
Frequently Asked Questions
What’s the difference between verifying who someone is versus that they are a real person? This is a great question because it gets to the heart of different security goals. Verifying who someone is involves confirming their legal identity, often by matching their face to a government-issued ID like a driver’s license. This is common in banking or other highly regulated industries. On the other hand, verifying that someone is a real person is about confirming personhood—proving there’s a live, unique human behind the screen, not a bot or a deepfake. This approach, used by technologies like VerifEye, is focused on preventing fraud and ensuring data integrity without collecting sensitive personal information, making it a more privacy-friendly option for many platforms.
Is a simple SMS code still a good enough verification method? While sending a code via SMS is familiar and widely used, its security is being increasingly questioned. Hackers can sometimes intercept text messages through techniques like SIM swapping, where they trick a mobile carrier into transferring a phone number to a device they control. For low-risk actions, SMS can still be a decent, low-friction option. However, for securing sensitive transactions or high-value accounts, you should consider stronger methods like push notifications to an authenticator app or biometric checks that confirm the user is physically present.
How much work is it for my developers to actually integrate a verification API? The level of effort really depends on the API provider you choose. The best ones are designed with developers in mind and offer clear, comprehensive documentation, code samples, and SDKs for popular programming languages. A well-documented API can be integrated in a matter of days, not weeks. The goal is for the provider to handle the complex backend infrastructure so your team can simply make a few API calls to add a powerful verification layer to your app without having to build it from scratch.
My app serves a global audience. How do I handle verification in different countries? This is a critical consideration for any growing platform. A top-tier verification API should have a global infrastructure that can reliably deliver codes or perform checks anywhere in the world. This means having relationships with different mobile carriers and understanding regional regulations. Look for a provider that offers flexible channels, like SMS, email, WhatsApp, and voice calls, as user preferences and channel reliability can vary significantly from one country to another. This flexibility ensures you can create a smooth and dependable verification experience for all your users, no matter their location.
When should I use a simple verification check versus a more advanced one like a biometric scan? The right method depends on the level of risk associated with the action a user is taking. For something low-risk, like signing up for a newsletter, a simple email verification is probably sufficient. For a higher-stakes action, like resetting a password or authorizing a large payment, you need more certainty. This is where you would use multi-factor authentication or an advanced biometric check to confirm liveness. The best strategy is often to use adaptive authentication, where the security challenge matches the risk level of the user’s action, creating a secure system that doesn’t add unnecessary friction.