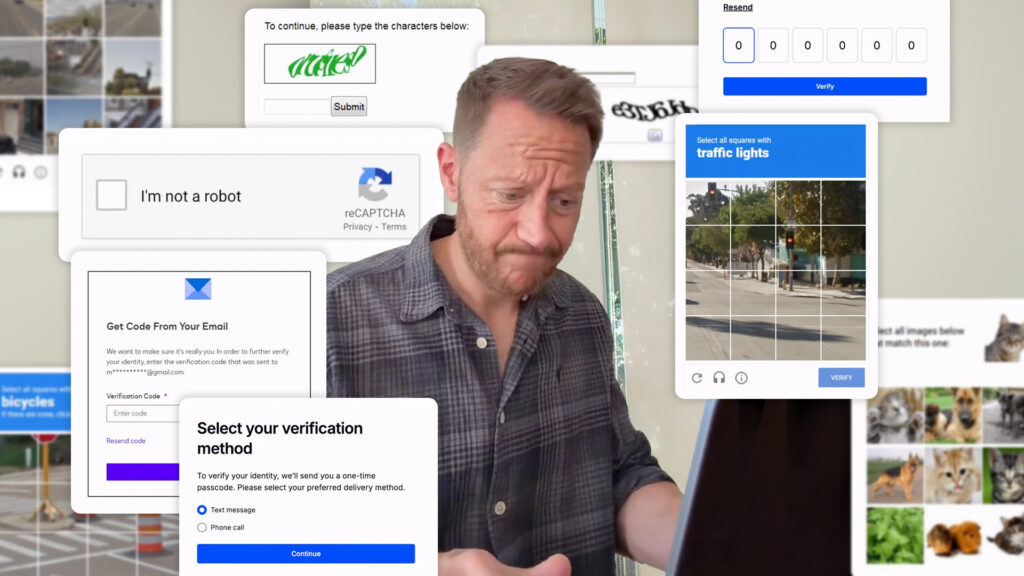
Actor Russell Parry has a gift for capturing shared misery with surgical precision. His recent Instagram reel, “Logging into anything in 2026”, dramatizes the full emotional arc of modern authentication in under a minute: the CAPTCHA demanding you identify traffic lights in a photo taken through a frosted window, the SMS code that arrives two minutes after the window closed, the email verification that goes to spam, the codes that never match, and finally — inevitably — the open window. The defenestration. The only rational response.
It’s a comedy. But behind the laughter is a very real, very costly problem that businesses everywhere are ignoring at their peril.
“26% of US adults abandon an online purchase because they’re forced through a cumbersome login process. Authentication friction isn’t an annoyance; it’s a revenue leak.”
The Authentication Experience is Broken
The frustration isn’t imagined, it’s quantified. Research from Baymard Institute found that 26% of US adults abandon an online purchase solely because they’re forced through a cumbersome login process. Gartner reports that 20–50% of all IT helpdesk calls relate to password resets, at an estimated $70 a reset. Meanwhile, Google’s research found that up to 10% of users fail SMS verification on the first attempt and CAPTCHA fares no better. A study in ACM CHI found image-based CAPTCHAs take an average of 9.8 seconds and are still solved incorrectly by real humans with alarming regularity. See our deep-dive: Is Your Bot Protection Hurting User Data Privacy?
A Scene-by-Scene Breakdown
Each moment in Parry’s reel maps to a real drop-off point:
The CAPTCHA Gauntlet
Bots now solve modern CAPTCHAs with greater accuracy than humans. What remains is pure friction for legitimate users and a growing privacy liability. The test no longer passes its own test.
The SMS Verification Trap
SMS-based MFA is vulnerable to SIM-swapping, SS7 exploits, and delivery delays. CISA has explicitly recommended organizations migrate away from it. And yet it persists. Costly, fragile, and maddening.
The Email & Code Verification Loop
The email is in spam. The code has expired. The new code doesn’t match. These aren’t edge cases, they’re the norm. Each one is a moment where a real user with genuine intent closes the tab and perhaps never comes back. In e-commerce, that’s lost revenue. In financial services, it’s failed onboarding. In healthcare, it’s a patient who didn’t access their records.
The Hidden Cost of Friction
Friction isn’t just an annoyance, it compounds across four dimensions:
- Abandonment:Conversion rates drop 20–40% when users hit unexpected verification steps.
- Support costs: Password resets, SMS gateway fees, and helpdesk time are a significant and avoidable overhead.
- Security paradox: Frustrated users reuse passwords, disable 2FA, and share credentials, the friction makes good security habits unsustainable.
- Brand damage: If signing in feels like a punishment, the product feels hostile.
For a broader view of where the industry is heading, see: Passwordless Authentication: Your Complete Guide
“Between 20% and 50% of all IT helpdesk calls relate to password resets costing enterprises an estimated $70 every single time.”
There is a Better Way: Introducing VerifEye MFA
What if authentication required nothing from the user except to look at their screen for a fraction of a second?
VerifEye MFA from Realeyes uses passive liveness detection to verify a real human is present at authentication, no codes, no SMS, no CAPTCHA, no traffic lights. At its core is a cryptographic hash: a one-way mathematical fingerprint generated from your biometric data at registration. Think of it as a padlock — the hash is the locked form, and it can never be reverse-engineered. Only the hash is stored, never the underlying data, so a breach yields nothing usable. Verification happens instantly, passively, in the background.
The result: authentication in under two seconds, with no conscious effort from the user, stronger security than SMS, and no gateway fees. For a technical deep-dive, see:
A Passive Liveness Check: How It Works & Why You Need It
What Is a Liveness Check and Why You Need One.
Key Advantages at a Glance
- Zero friction: Under two seconds, no user action required, no drop-off at the login gate.
- Stronger security: A stolen password is useless without its owner’s live face. SIM-swapping attacks become irrelevant.
- Lower cost than SMS: No gateway fees, no re-sends, no per-verification cost at scale.
- Privacy-first: Only the cryptographic hash is stored — no sensitive facial data, fully GDPR-compliant.
- No new hardware: Works with the camera already on every smartphone, laptop, and tablet.
“VerifEye MFA uses a cryptographic hash, a one-way mathematical fingerprint so there’s no sensitive data to steal, no SMS code to intercept, and nothing for the user to do except look at their screen.”
Integration: Works With Your Existing Stack
VerifEye MFA slots into existing infrastructure without wholesale replacement. It integrates with Auth0, Okta, Azure Active Directory, and AWS Cognito out of the box, and connects to custom systems via a clean REST API. SDKs are available for web, iOS, and Android and most teams are live within days. For organizations already on passkeys, VerifEye MFA adds a liveness layer on top; see Passkey Authentication for Web Applications for how the two approaches complement each other.
From Comedy to Competitive Advantage
Russ Parry’s reel is funny because it’s so true, but it also represents a genuine opportunity. Authentication is a moment of high intent. Friction here is an own goal: it costs money, damages trust, and sends users to the open window.
The organizations that win on experience are those that make access feel effortless without sacrificing security. That’s not a futuristic concept. It’s available now.
Ready to eliminate authentication friction? Explore VerifEye MFA and see how passive liveness detection can transform your user experience, without compromising on security.